Amazon RDS for SQL Server Destination Setup Guide
Follow our setup guide to connect Amazon RDS for SQL Server database as a destination to Fivetran.
Prerequisites
To connect Amazon RDS for SQL Server to Fivetran, you need the following:
- SQL Server Version 2012 or above
- IP (for example,
1.2.3.4) or host (your.server.com) - Port (usually
1433) - Access to your SQL Server through Fivetran's IPs for your database's region
- A Fivetran-specific SQL Server user with WRITE-level permissions
- A Fivetran user account with permissions to create or manage destinations
We only support the Enterprise and Standard editions of SQL Server.
Setup instructions
Choose your deployment model
Before setting up your destination, decide which deployment model best suits your organization's requirements. This destination supports both SaaS and Hybrid deployment models, offering flexibility to meet diverse compliance and data governance needs.
See our Deployment Models documentation to understand the use cases of each model and choose the model that aligns with your security and operational requirements.
You must have an Enterprise or Business Critical plan to use the Hybrid Deployment model.
Choose connection method
Decide whether to connect to your Amazon RDS for SQL Server database directly, using an SSH tunnel, or using AWS PrivateLink. For more information, see our destination connection options documentation.
Connect directly
If you connect directly, you must create a rule in a security group that allows Fivetran access to your database instance and port.
Configure your firewall and/or other access control systems to allow incoming connections to your host and port from Fivetran's IPs for your database's region.
Connect using an SSH tunnel
If you connect using an SSH tunnel, Fivetran connects to a separate server in your network that provides an SSH tunnel to your Amazon RDS for SQL Server database. You must then configure your tunnel server's security group to allow Fivetran access and configure the instance's security to allow access from the tunnel.
You must connect through SSH if your destination is contained within an inaccessible subnet.
To connect using SSH, do the following:
In the destination setup form, select the Connect via an SSH tunnel option.
Copy Fivetran's public SSH key.
Add the public key to the
authorized_keysfile of your SSH server. The key must be all on one line, so make sure that you don't introduce any line breaks when cutting and pasting.
Connect using AWS PrivateLink
You must have a Business Critical plan to use AWS PrivateLink.
AWS PrivateLink allows VPCs and AWS-hosted or on-premises services to communicate with one another without exposing traffic to the public internet. PrivateLink is the most secure connection method. Learn more in AWS’ PrivateLink documentation.
Follow our AWS PrivateLink setup guide to configure PrivateLink for your destination.
Connect using Proxy Agent
Fivetran connects to your destination host through the Proxy Agent, providing secure communication between Fivetran processes and your warehouse host. The Proxy Agent is installed in your network and creates an outbound network connection to the Fivetran-managed SaaS.
To learn more about the Proxy Agent, how to install it, and how to configure it, see our Proxy Agent documentation.
Configure VPC security group
Configure your Virtual Private Cloud (VPC) Security Groups and Network Access Control Lists (ACLs) to allow incoming connections to your SQL server host and port from your SSH tunnel server's IP address.
The following instructions assume that your instance is in a VPC. If your database instance is not in a VPC, you can still use these instructions because configuring a non-VPC security group is an almost identical process.
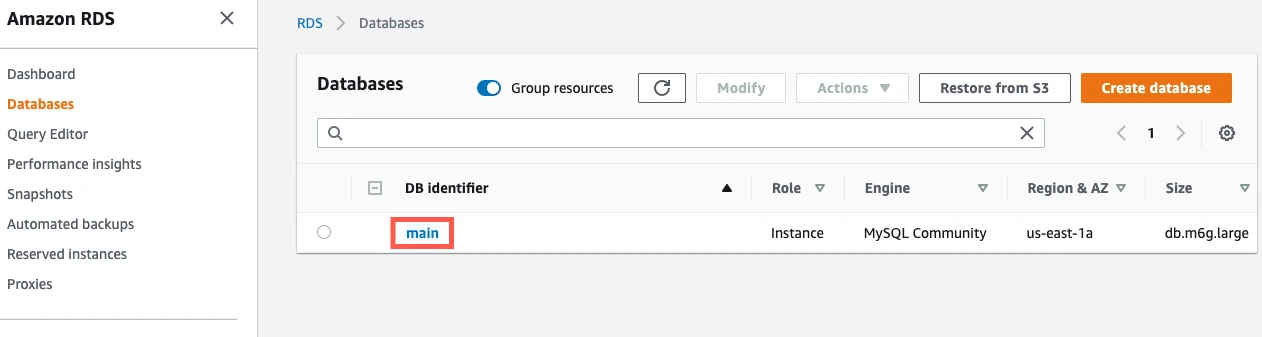
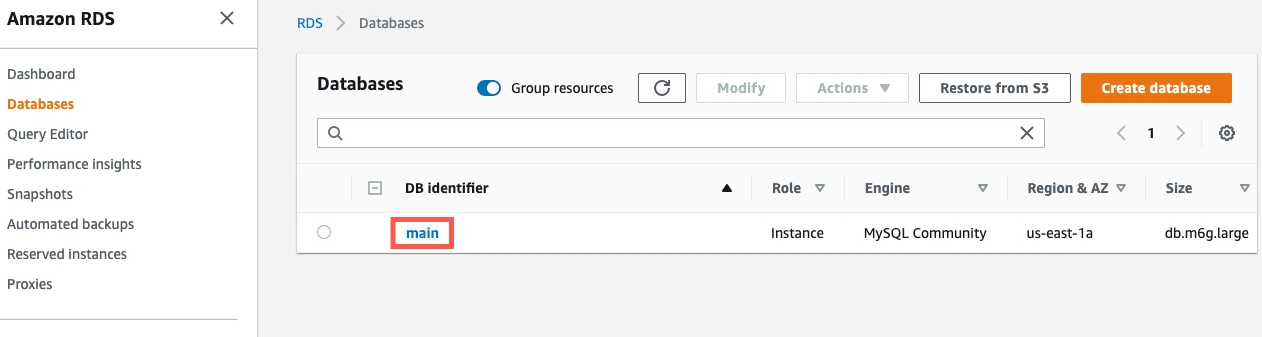
Log in to your RDS dashboard.
In the Databases pane, expand the view on the instance.
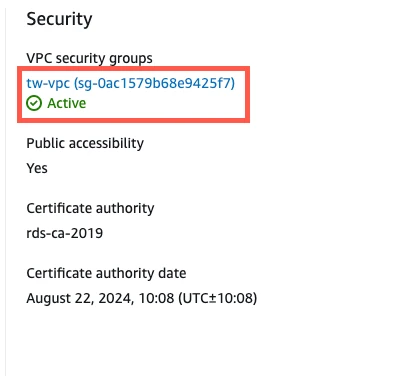
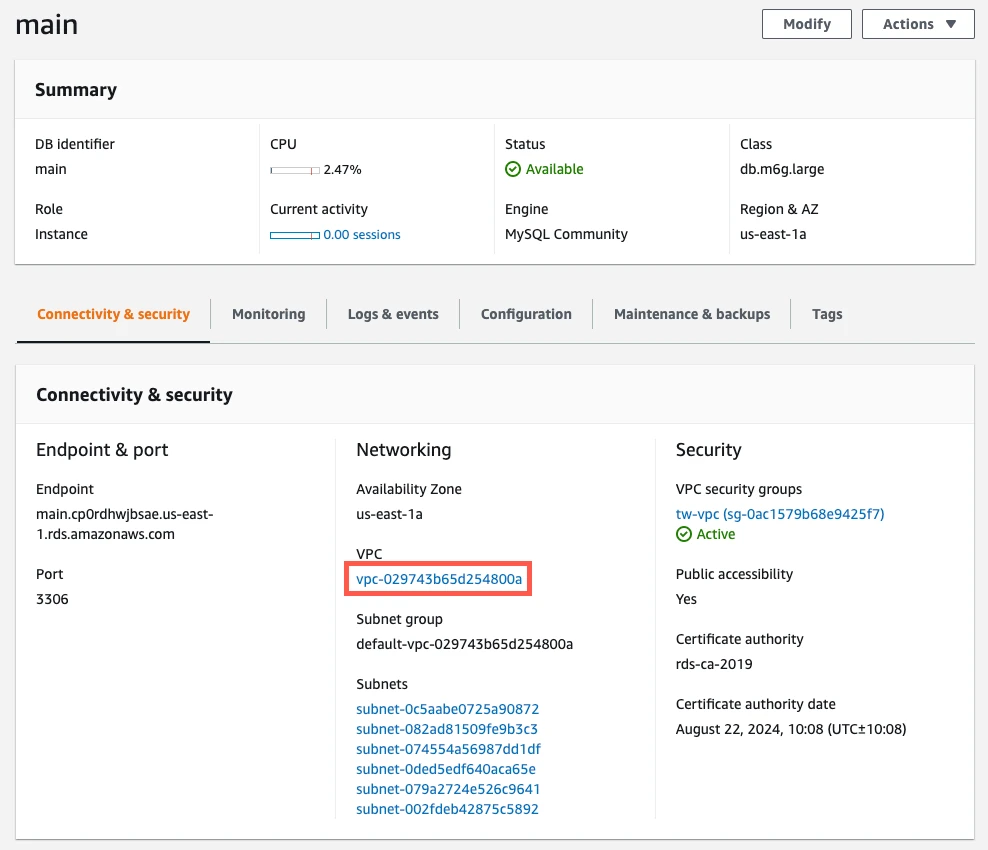
On the Details page, check that the Publicly accessible field is set to Yes.
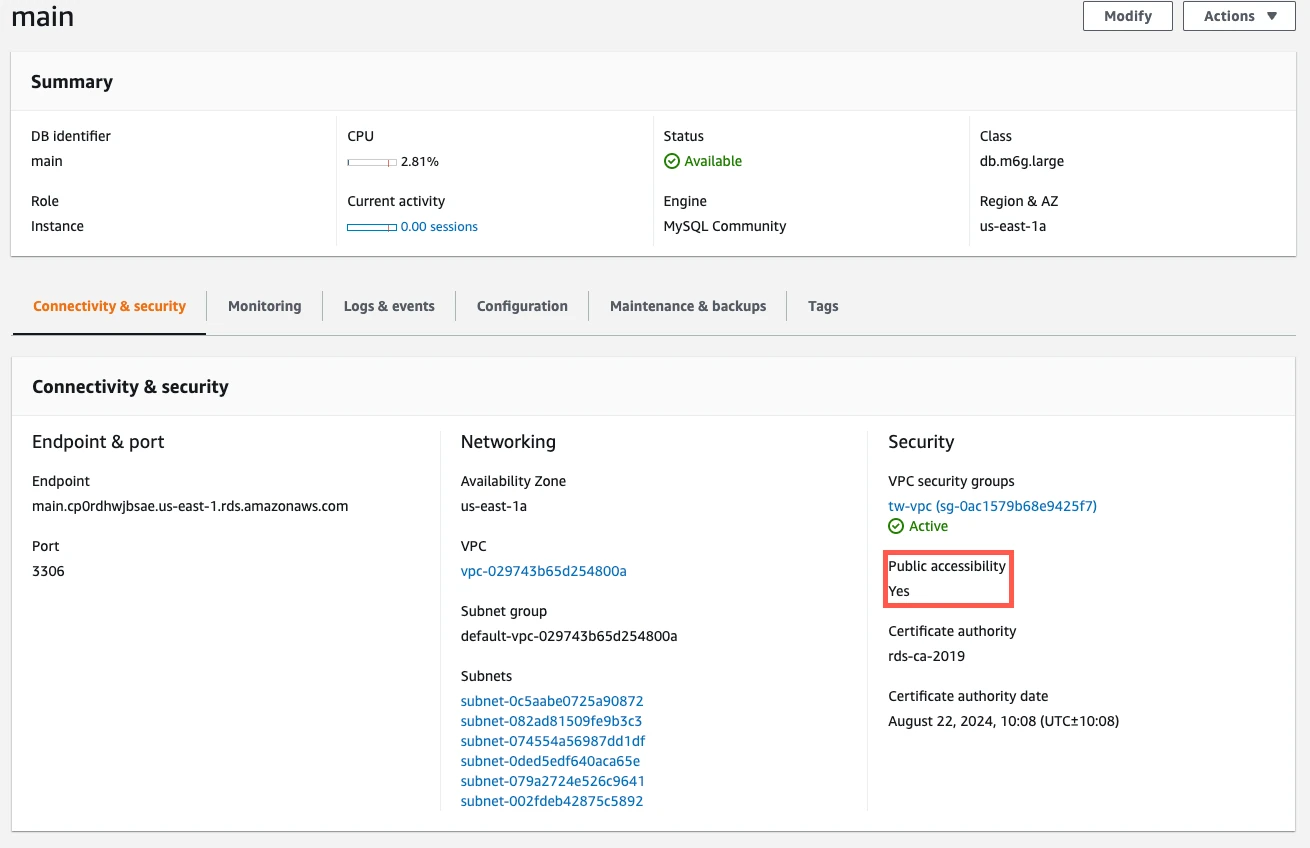
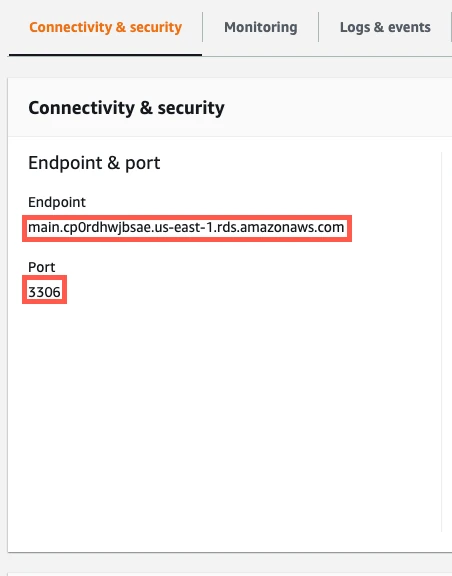
Make a note of the Endpoint and Port number. You will need them to configure Fivetran.
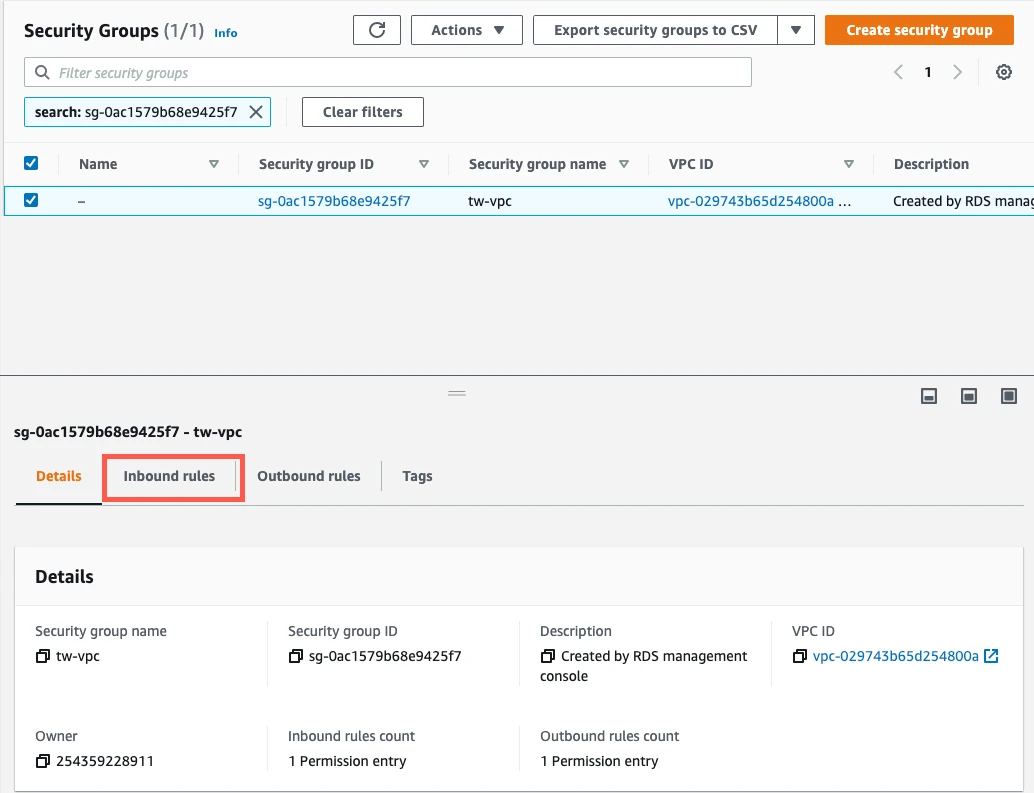
Click the VPC security groups link.
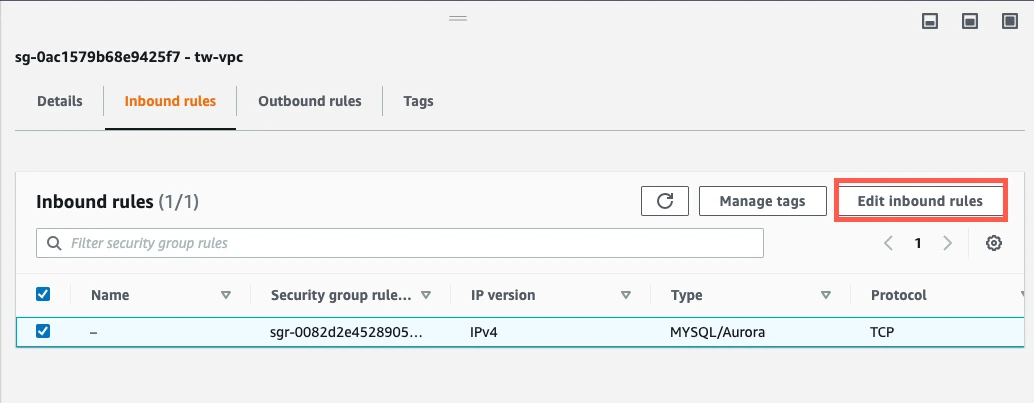
In the Security Groups section, go to the Inbound rules tab.
Click Edit inbound rules.
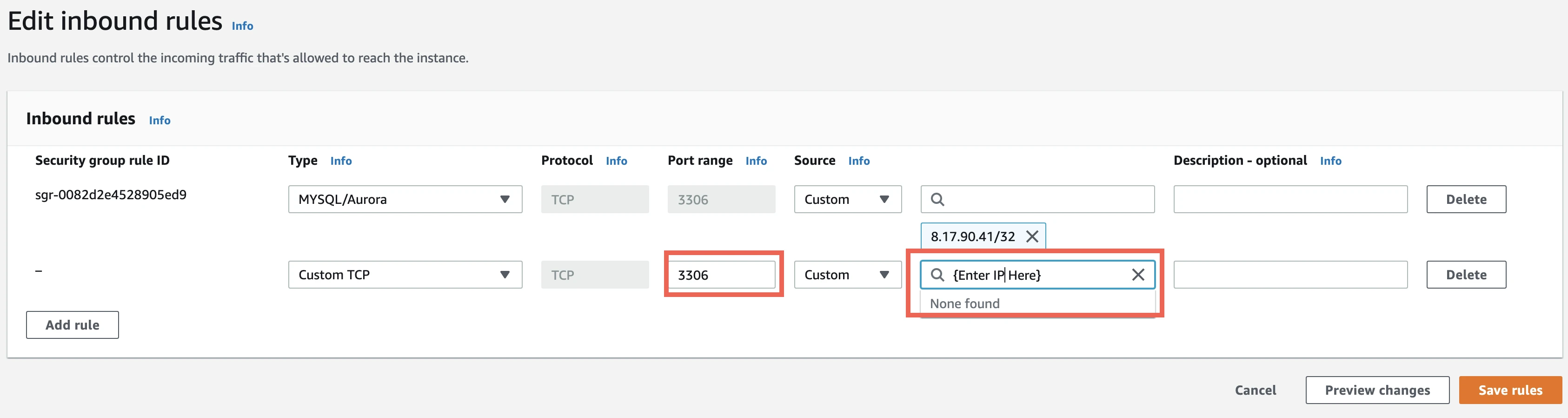
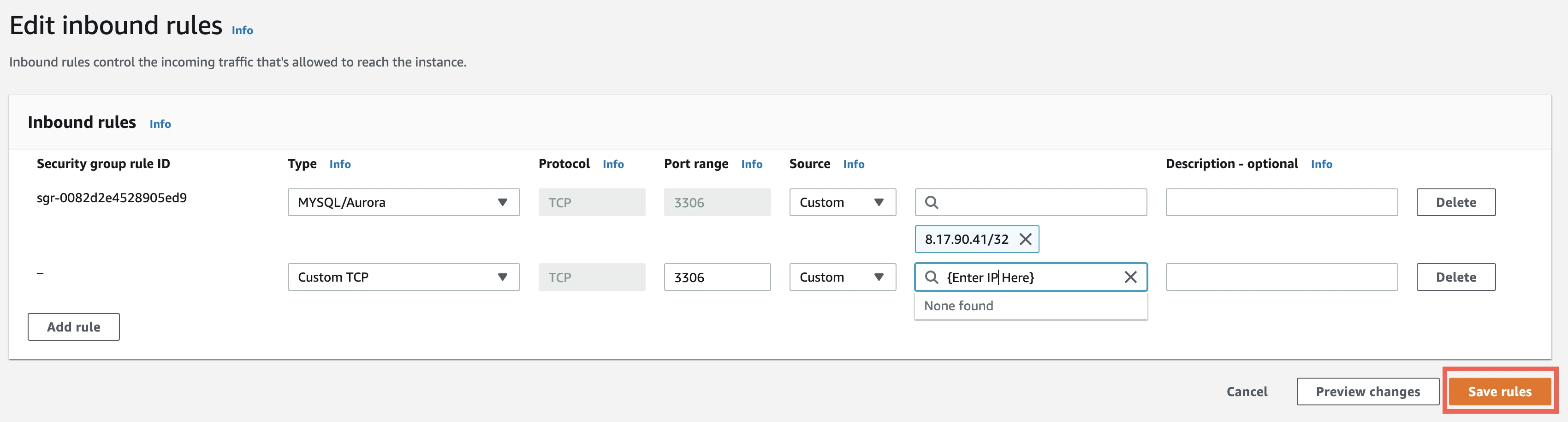
Enter the following details:
- In the Port Range field, enter the port number that you found earlier
- In the Source field, select Custom IP and then enter Fivetran's IPs
Click Save rules.
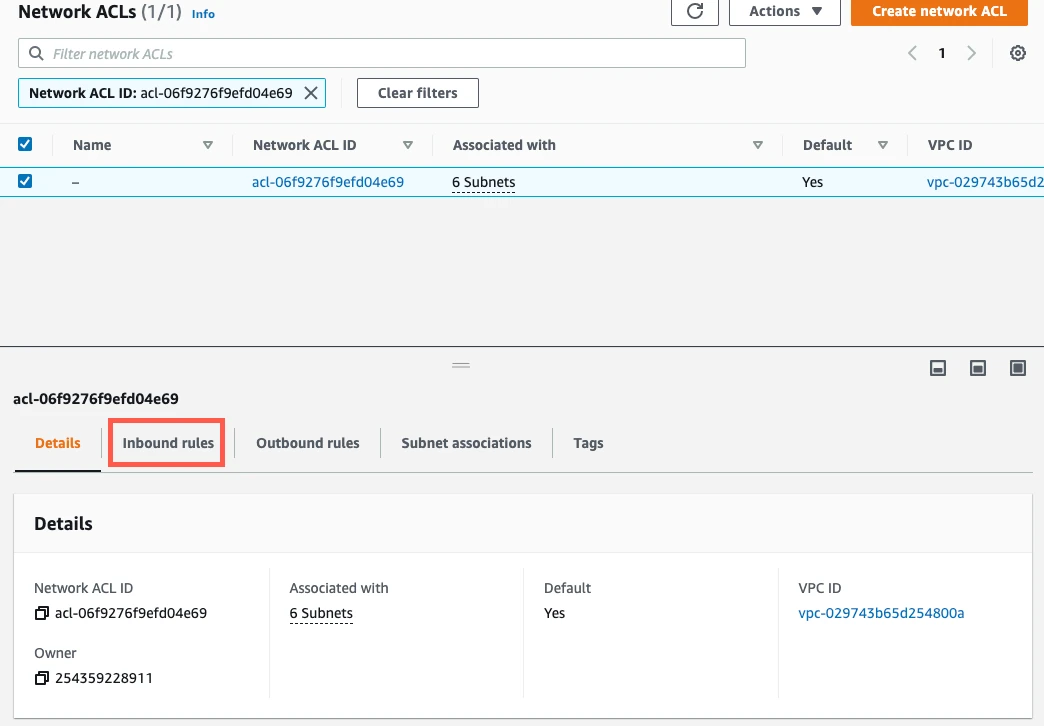
Configure Network ACLs
Return to the RDS Dashboard and expand the view on the instance.
In the Details page, click the VPC link.
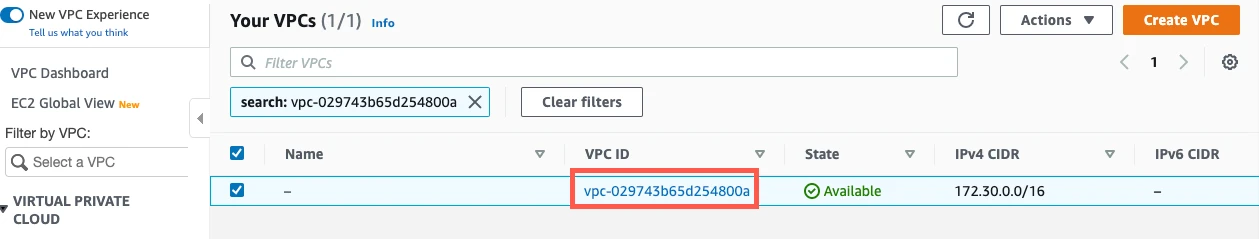
Select the VPC ID link.
In the Summary tab, click the Main network ACL link.
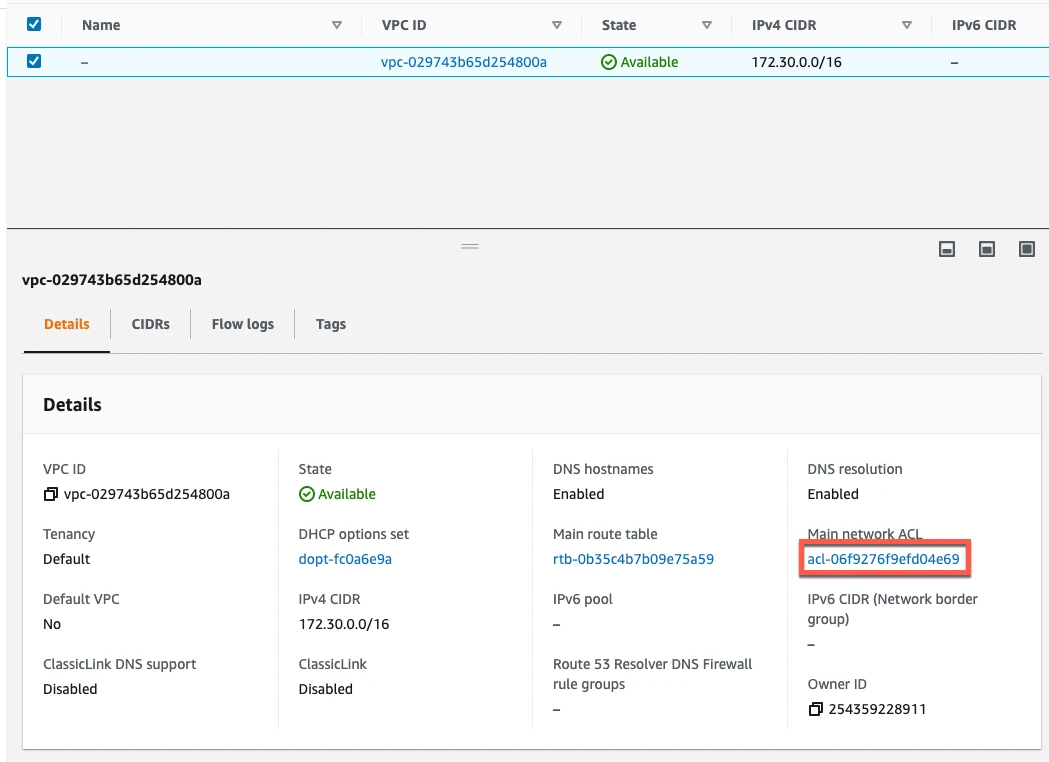
You must edit both the Inbound and Outbound rules.
Go to the Inbound Rules tab.
If you have a default VPC that was automatically created by AWS, then the settings already allow all incoming traffic as indicated by the Source value
0.0.0.0/0and the fact that the ALLOW entry is listed above the DENY entry.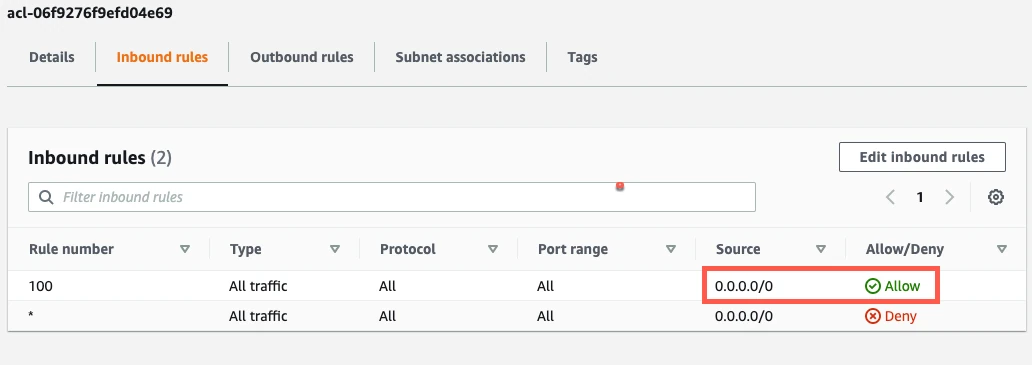
If your inbound rules don't include an
ALL - 0.0.0.0/0 - ALLOWentry, click Edit to edit the rules to allow{your-ssh-tunnel-server-ip-address}/32to access the port number of your read replica (usually1433).
For additional help, see Amazon's Network ACLs documentation.
Go to the Outbound Rules tab.
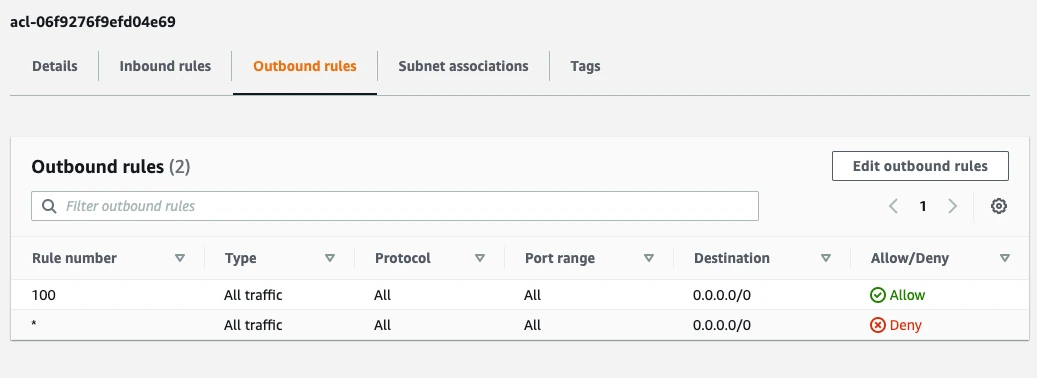
- If your outbound rules don't include an
ALL - 0.0.0.0/0 - ALLOWentry, click Edit to edit the rules to allow outbound traffic to all ports1024-65535for Destination{your-ssh-tunnel-ip-address}/32.
- If your outbound rules don't include an
Create Fivetran user
Connect to your SQL Server database as an Admin user and execute the following commands to create a user for Fivetran. Choose a memorable username (for example, fivetran). Replace <database> with the name of your database and <password> with a password of your choice:
USE [<database>]; CREATE LOGIN fivetran WITH PASSWORD = '<password>'; CREATE USER fivetran FOR LOGIN fivetran;
Grant permissions
Execute the following commands to grant the fivetran user CREATE permission for the database you would like Fivetran to sync:
GRANT CREATE SCHEMA TO fivetran; GRANT CREATE TABLE TO fivetran;
Complete Fivetran configuration
Log in to your Fivetran account.
Go to the Destinations page and click Add destination.
Enter a Destination name of your choice and then click Add.
Select Amazon RDS for SQL Server as the destination type.
(Enterprise and Business Critical accounts only) Select the deployment model of your choice:
- SaaS Deployment
- Hybrid Deployment
If you selected Hybrid Deployment, click Select Hybrid Deployment Agent and do one of the following:
- To use an existing agent, select the agent you want to use, and click Use Agent.
- To create a new agent, click Create new agent and follow the setup instructions specific to your container platform.
Enter the Host name you found in Step 3.
Enter the Port number you found in Step 3.
Enter the User name you created in Step 5.
Enter your Password.
Enter the Database name you want to replicate to.
(Not applicable to Hybrid Deployment) Choose your Connection method:
- Connect directly
- Connect via an SSH
- Connect via Private Networking
- Connect using Proxy Agent
The Connect via Private Networking option is available only for Business Critical accounts.
If you choose Connect via an SSH tunnel, enter the following details:
- SSH Host
- SSH Port
- SSH User
- (Optional) If you enabled TLS on your database in Step 2, make sure to keep the Require TLS through Tunnel toggle turned ON.
(Not applicable to Hybrid Deployment) Choose the Data processing location. Depending on the plan you are on and your selected cloud service provider, you may also need to choose a Cloud service provider and cloud region as described in our Destinations documentation.
If you are using AWS PrivateLink, select AWS in the Cloud service provider drop-down menu.
Choose your Time zone.
(Optional for Business Critical accounts and SaaS Deployment) To enable regional failover, set the Use Failover toggle to ON, and then select your Failover Location and Failover Region. Make a note of the IP addresses of the secondary region and safelist these addresses in your firewall.
Click Save & Test.
Fivetran tests and validates the Amazon RDS for SQL Server destination connection. On successful completion of the setup tests, you can sync your data using Fivetran connectors to the Amazon RDS for SQL Server destination.
In addition, Fivetran automatically configures a Fivetran Platform connection to transfer the connection logs and account metadata to a schema in this destination. The Fivetran Platform Connector enables you to monitor your connections, track your usage, and audit changes. The Fivetran Platform connection sends all these details at the destination level.
If you are an Account Administrator, you can manually add the Fivetran Platform connection on an account level so that it syncs all the metadata and logs for all the destinations in your account to a single destination. If an account-level Fivetran Platform connection is already configured in a destination in your Fivetran account, then we don't add destination-level Fivetran Platform connections to the new destinations you create.
Setup tests
Fivetran performs the following Amazon RDS for SQL Server connection tests:
The Proxy Agent Status Test checks if the Proxy Agent is running and connected to Fivetran. We skip this test if you are not connecting using a Proxy Agent.
The SSH Tunnel Test validates the SSH tunnel details you provided in the setup form and then checks the connectivity to the instance using the SSH Tunnel if you are connecting using an SSH tunnel.
The Database Host Connection Test validates the database credentials you provided in the setup form. The test verifies that the host is not private and then checks the connectivity to the host.
The Database Certificate Validation Test generates a pop-up window where you must choose which certificate you want Fivetran to use. The test then validates that certificate and checks that we can connect to your database using TLS. We skip this test if you aren't connecting directly.
The SQL Server Connection Test checks if we can access your database.
The Permission Test checks that we have the correct permissions to create schemas and tables in your database.
The SQL Server Type Test validates the SQL Server service type. The test checks if your SQL Server implementation matches the destination type. For example, this test will fail if you try to set up an Amazon RDS for SQL Server destination using a generic SQL Server database.
The tests may take a couple of minutes to finish running.