Google Cloud SQL for MySQL Setup Guide
Follow these instructions to replicate your Google Cloud SQL for MySQL database to your destination using Fivetran.
Prerequisites
To connect your MySQL database to Fivetran, you need:
- MySQL version 5.6 or above.
- Your database host's IP (for example,
1.2.3.4) or domain (your.server.com) - Your database's port (usually
3306) - TLS enabled on your database (if you want to connect to Fivetran directly)
- A unique replica ID for Fivetran. We need this ID because we connect to your database as a replica. We provide a random replica ID in your setup form, but you can provide your own if you'd prefer or if the form's replica ID conflicts with one of your existing replica IDs.
The replica ID is a unique ID within the MySQL replica set. By default, the replica ID is a random integer greater than 1000.
If you will be using binary log as your incremental sync method, note Google Cloud SQL for MySQL automatically manages its binary log retention period. By default, binary logs are purged after 7 days. If your connection is paused for more than 7 days, you may be required to re-sync your data.
For the prerequisites for connecting using an SSH tunnel, see Fivetran's Connection Options page.
Setup instructions
Choose connection method
Decide whether to connect Fivetran to your MySQL database directly, using a Google Cloud Virtual Machine, using Google Cloud Private Service Connect, or using Proxy Agent.
Connect directly (TLS required)
You must have TLS enabled on your database to connect directly to Fivetran. Follow Google Cloud's TLS setup instructions to enable TLS on your database.
Fivetran connects directly to your MySQL database. This is the simplest method.
To connect directly, configure your firewall and/or other access control systems to allow incoming connections to your MySQL host and port (usually 3306) from Fivetran's IPs for your database's region.
Connect through Google Cloud Virtual Machine
Create a Google Cloud Virtual Machine to act as a proxy to connect using one of these options:
- SSH tunneling with client certificates configured
- Google Cloud SQL Proxy
- Certificate forwarding using stunnel
Connect using Google Cloud Private Service Connect
You must have a Business Critical plan to use Google Cloud Private Service Connect.
Google Cloud Private Service Connect allows VPCs and Google-hosted or on-premises services to communicate with one another without exposing traffic to the public internet. Learn more in Google Cloud's Private Service Connect documentation.
Follow our Google Cloud Private Service Connect setup guide to configure Private Service Connect for your database.
Connect using Proxy Agent
Fivetran connects to your database through the Proxy Agent, providing secure communication between Fivetran processes and your database host. The Proxy Agent is installed in your network and creates an outbound network connection to the Fivetran-managed SaaS.
To learn more about the Proxy Agent, how to install it, and how to configure it, see our Proxy Agent documentation.
Choose incremental sync method
To keep your data up to date after the initial sync, we use one of the following incremental sync methods:
- Binary log
- Fivetran Teleport Sync
Fivetran Teleport Sync disables large, rapidly changing tables if they fail to sync. Learn more in the Teleport general limitations documentation.
Each of these methods keeps a record of recent data changes, which allows Fivetran to update only the data that has changed since our last sync.
To learn the differences between the two methods, see our incremental sync documentation.
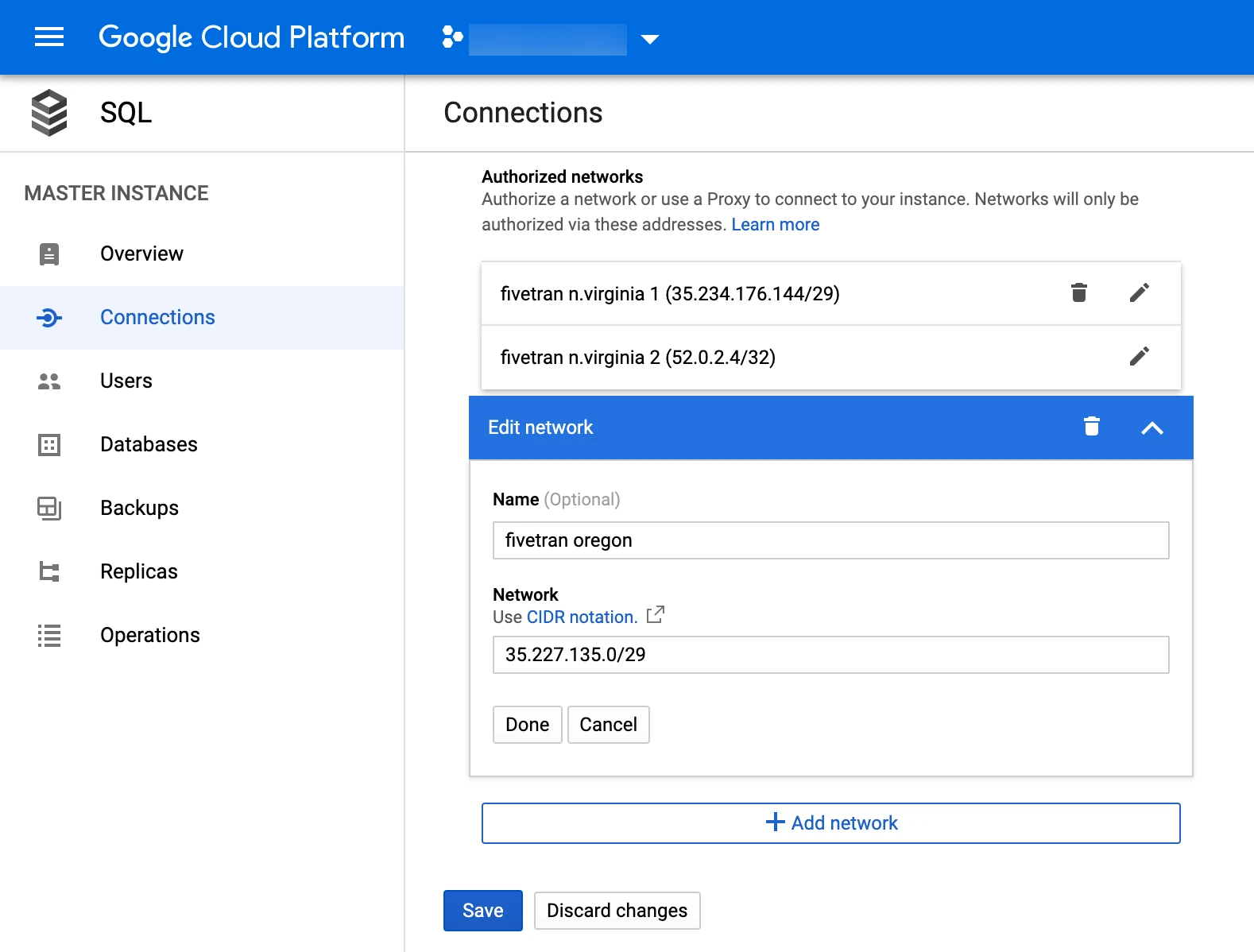
Allow access
Your Google Cloud SQL for MySQL primary or replica server needs to be made accessible to Fivetran's data processing server.
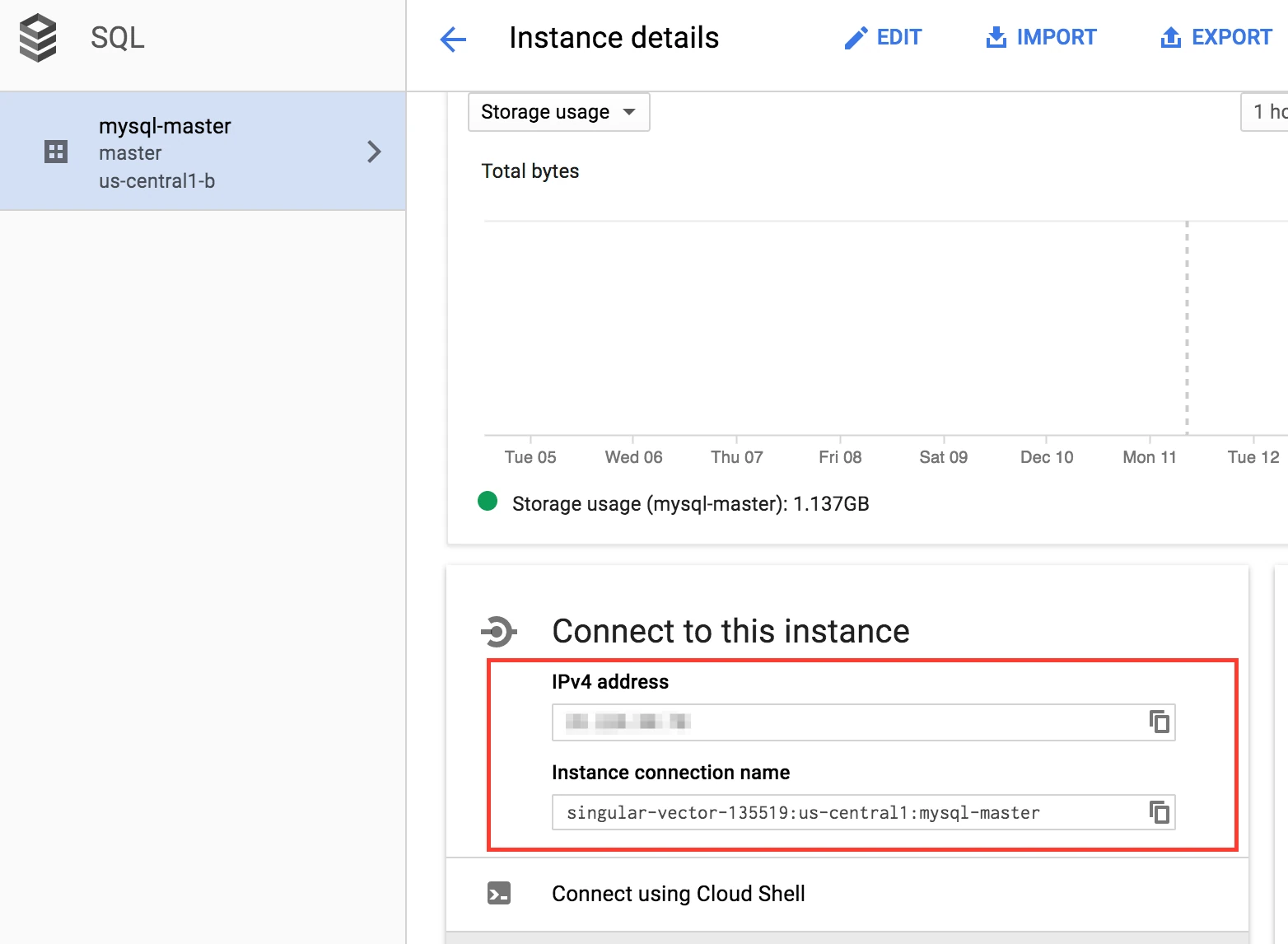
In your MySQL Dashboard, select the "Master" instance you would like to use.
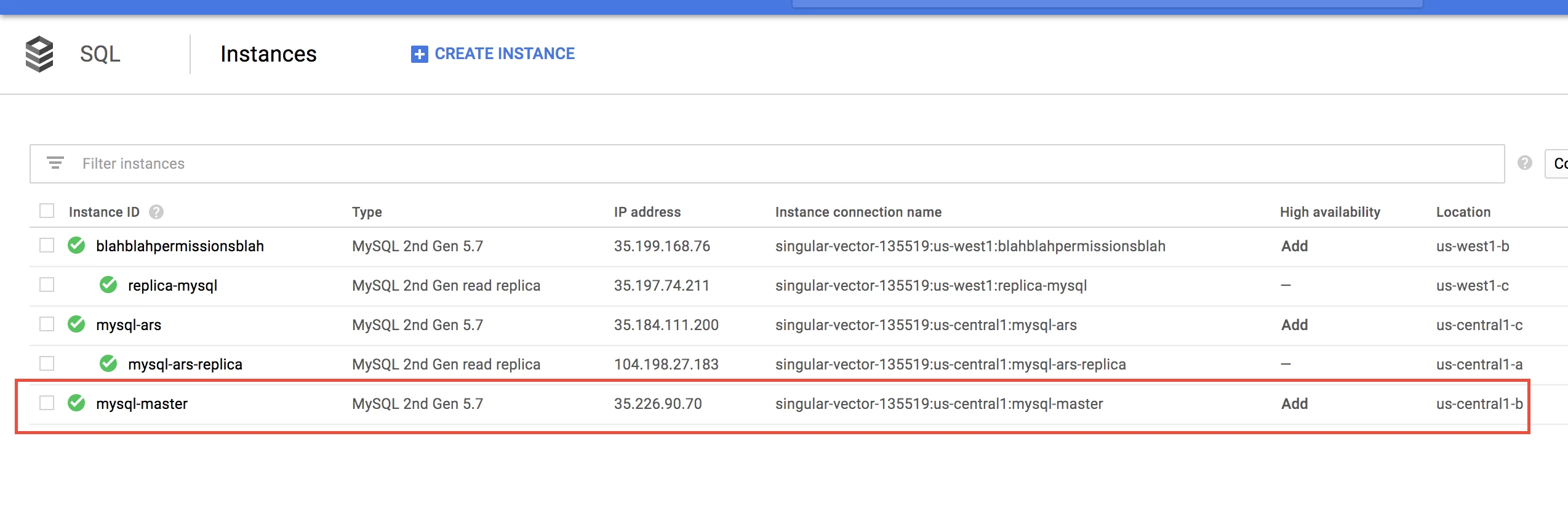
If you're using a replica, select Replicas from the left menu, then choose the Replica instance that you want to connect to Fivetran.
Note the Master or Replica IP address and port number (3306 by default).
Add Fivetran's IP addresses to access the port number of your primary or replica node unless you already have 0.0.0.0/0 as an allowed network.
Create user and configure incremental updates
Next, you must create a Fivetran user in your Google Cloud SQL for MySQL database. Make sure to do this on the primary node because replicas are read-only.
This user must be reserved for Fivetran use only and must be unique to your connection. For more information, see our MySQL documentation.
How you create a user depends on which incremental sync method you are using. Follow the instructions below for your incremental sync method Step 2:
Binary log
Open a connection to your Google Cloud SQL for MySQL database using your favorite SQL tool (for example, MySQL Workbench or the "mysql" command in your operating system's terminal window).
Create a Fivetran user and grant replication permissions by running the following SQL commands. Replace
<username>andpasswordwith a username and password of your choice.CREATE USER '<username>'@'%' IDENTIFIED BY 'password'; GRANT SELECT, REPLICATION CLIENT, REPLICATION SLAVE ON *.* TO '<username>'@'%';
You must grant the Fivetran user SELECT permissions for all of the columns in the tables that you want to sync. When we do not have SELECT access to all columns in a table, we trigger a re-sync for that table, which slows down your syncs. If you don't want to sync certain columns, you can exclude them from your syncs in the Fivetran dashboard.
Check that binary logging is enabled (optional)
By default, Google enables binary logging through point-in-time recovery for MySQL primary databases. To confirm that binary logging is enabled on your database, follow the steps below.
If you are using a read replica, you must enable binary logging in your read replica. Read Google Cloud's Replication in Cloud SQL documentation to see which databases support enabling binary logging on read replicas and the Point-in-time recovery documentation to learn how to enable it.
In your MySQL Dashboard, click Backups in the left menu.
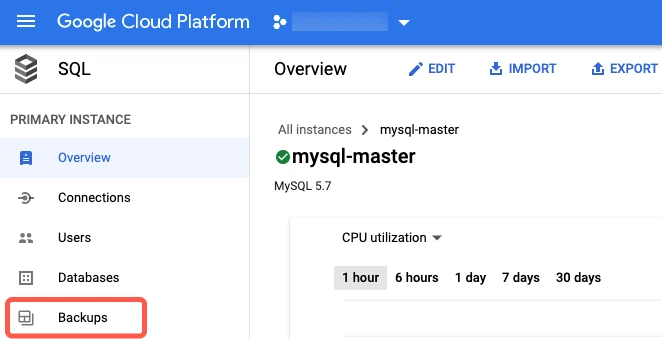
In the Settings section, confirm that Enable point-in-time recovery is set to Enabled.
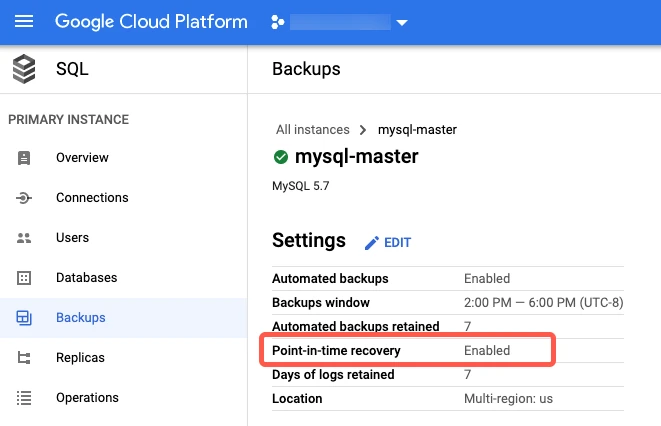
If point-in-time recovery is disabled, you must enable it. Click Edit.
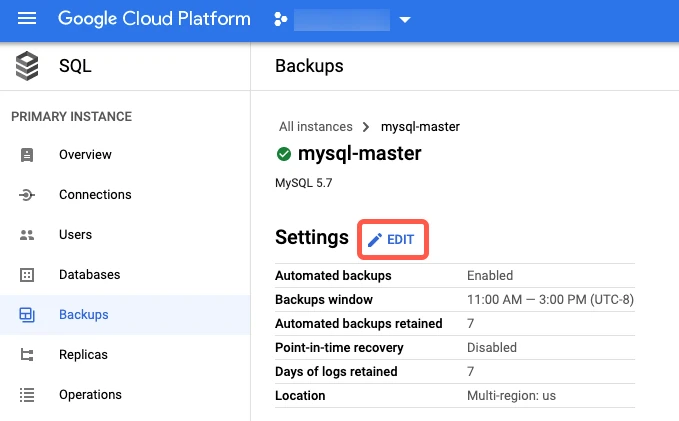
In the Edit backups settings window, select the Enable point-in-time recovery box to enable binary logging.
Click Save.
Your Cloud SQL instance will restart when you enable point-in-time recovery.
Fivetran Teleport Sync
Open a connection to your MySQL primary database using your favorite SQL tool (for example, MySQL Workbench or the
mysqlcommand in your operating system's terminal window).Create a Fivetran user and grant SELECT permissions by running the following SQL commands. Replace
<username>andpasswordwith a username and password of your choice.CREATE USER '<username>'@'%' IDENTIFIED WITH mysql_native_password BY 'password'; -- Option 1: Grant user SELECT permission on all tables and columns GRANT SELECT ON *.* TO '<username>'@'%'; -- Option 2: Grant user SELECT permission on only specified table and columns GRANT SELECT ON <tables/columns> TO '<username>'@'%';
Finish Fivetran configuration
In your connection setup form, enter a Destination schema prefix. This is used as the connection name and cannot be modified once the connection is created.
In the Destination schema names field, choose the naming convention you want Fivetran to use for the schemas, tables, and columns in your destination:
- Source naming: Preserves the original schema, table, and column names from the source system in your destination, and ignores the Destination schema prefix specified in the setup form. However, when multiple connections share the same source schema name (for example,
public), Fivetran stores their tables in the same destination schema. Tables with duplicate names may lead to overwrites and data inconsistencies. Be sure to use unique table names across connections that write to the same schema. - Fivetran naming: Standardizes the schema, table, and column names in your destination according to the Fivetran naming conventions.
If you want to modify your selection, make sure you do it before you start the initial sync.
Depending on your selection, we will either prefix the connection name to each replicated schema or use the source schema names instead.
- Source naming: Preserves the original schema, table, and column names from the source system in your destination, and ignores the Destination schema prefix specified in the setup form. However, when multiple connections share the same source schema name (for example,
(Hybrid Deployment only) If your destination is configured for Hybrid Deployment, the Hybrid Deployment Agent associated with your destination is pre-selected for the connection. To assign a different agent, click Replace agent, select the agent you want to use, and click Use Agent.
(Not applicable to Hybrid Deployment) Choose your connection method. If you selected Connect via an SSH tunnel, provide the following information:
- SSH hostname (do not use a load balancer's IP address/hostname)
- SSH port
- SSH user
- If you enabled TLS on your database in Step 1, make sure to keep the Require TLS through Tunnel toggle turned ON.
In the Host field, enter your database host's IP (for example,
1.2.3.4) or domain (for example,your.server.com)In the Port field, enter your database instance's port number (usually
3306).In the User field, enter the Fivetran-specific user that you created in Step 4.
In the Password field, enter the password for the Fivetran-specific user that you created in Step 4.
(Optional for Hybrid Deployment) If you want to use a TLS connection between your Hybrid Deployment Agent and Fivetran cloud, set the Require TLS toggle to ON.
Before you set this toggle to ON, you must first enable TLS on your database. Learn how in the Security section of the MySQL reference manual for your database version.
Under Update Method, choose how Fivetran will detect data changes in your source database:
- Read Changes via Binary Log - Reads directly from the MySQL binary log using Fivetran's Binary log incremental sync method.
- Detect Changes via Fivetran Teleport Sync - Detects changes by comparing source and snapshot data using Fivetran Teleport Sync incremental sync method.
(Binary log only) Enter a unique Replica ID for Fivetran. We provide a random replica ID, but you can provide your own if you'd prefer or if the setup form's replica ID conflicts with one of your existing replica IDs.
(Not applicable to Hybrid Deployment) Copy the Fivetran's IP addresses (or CIDR) that you must safelist in your firewall.
Click Save & Test. Fivetran tests and validates our connection to your Google Cloud SQL for MySQL database. Upon successful completion of the setup tests, you can sync your data using Fivetran.
Setup tests
Fivetran performs the following tests to ensure that we can connect to your Google Cloud SQL for MySQL database and that it is properly configured:
- The Connecting to SSH Tunnel Test validates the SSH tunnel details you provided in the setup form. It generates a pop-up window where you must verify the SSH fingerprint. It then checks that we can connect to your database using the SSH Tunnel. (We skip this test if you are connecting directly.)
- The Connecting to Host Test verifies that the database host is not private and checks that we can connect to the host.
- The Validating TLS Connection to Source Database Test validates the server certificate and checks that we can connect to your database using TLS. An untrusted certificate generates a pop-up window where you must choose which certificate you want Fivetran to use. (We skip this test if you selected an indirect connection method and then disabled the Require TLS through Tunnel toggle.)
- The Validating Database User Test validates the database credentials you provided in the setup form.
- (Binary log only) The Checking Database Configuration Test verifies that we can find your database's server ID. It then checks your binary log configuration and confirms that we can connect to the binary log.
- The Validating Database Type Test checks that your database type matches the connector type. For example, this test will fail if you try to set up a Google Cloud SQL for MySQL connection with a Amazon RDS for MySQL database. To perform this test, the Fivetran user needs permission to access the
mysqlsystem database, though we do not sync any data from that DB.
The tests may take a few minutes to finish running.