Customer-Managed Keys
Learn about customer-managed keys for your Business Critical account.
You must have a Business Critical plan to use customer-managed keys.
With customer-managed keys, you control the master key we use to encrypt your credentials and temporary data.
You have two ways to control access:
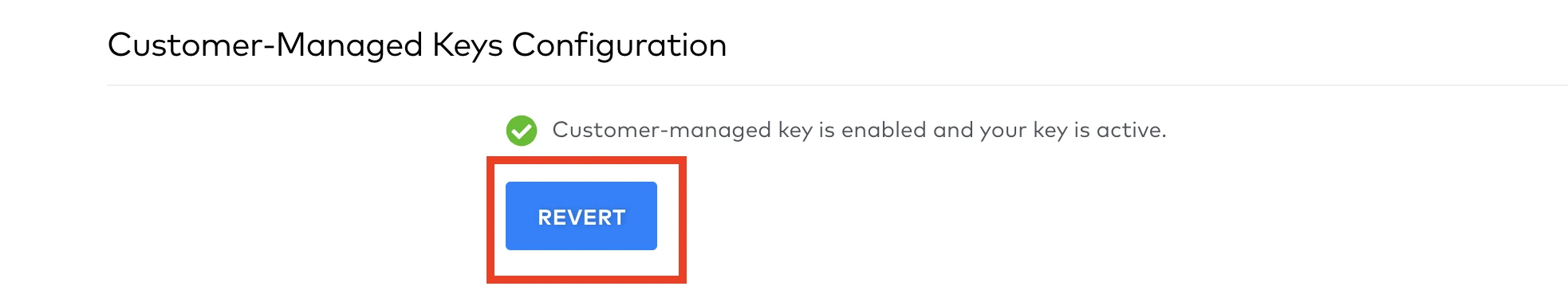
Revert in the Fivetran dashboard to roll back from customer-managed key encryption to Fivetran-managed encryption (for example, to rotate/replace a key). Reverting removes the CMK configuration from Fivetran and does not delete the key resource in your environment. To use CMK again, you add/configure a key again in the Fivetran dashboard.
In your cloud provider account, find the key and disable it. You can enable the key again later to restore our access and resume syncs, and you do not need to change any configuration in the Fivetran dashboard if you disable the key in your cloud provider.
We use keys from one of the following key management services (KMSs) to power this feature:
See our Data and Credential Encryption documentation to learn how we use customer-managed keys to encrypt data and credentials.
Setup guide
Customer-managed keys require additional setup. See the setup guide for your chosen provider:
- AWS customer-managed keys setup guide
- Azure customer-managed keys setup guide
- Google Cloud Platform (GCP) customer-managed key setup guide
Compromised keys
If you think your existing key has been compromised, do not delete the key before you have configured the new key to use with Fivetran. If you delete the compromised key, all connections in the destination that use credentials encrypted by that key will break.
Instead, do the following to correct your compromised key:
Revert the encryption with the current key.
Create a new key. That implies rotating the compromised key manually in AWS KMS or Azure Key Vault.